Prude Model – how solid it really is?
The Purdue Enterprise Reference Architecture is now the primary reference model on which OT security teams rely. And while Purdue was not developed as a security model, by mapping the high-level interrelationships and interdependencies between the high-level components of typical industrial control systems (ICSs). It has provided important guidance for protecting OT systems. Today, however, the deployment of many IT systems into OT environments has raised questions about the continued relevance of Purdue’s ICS model.
As a reminder. Purdue’s current architecture models OT and IT into six functional levels:
- Level 0 – Physical Process: This is the physical equipment that actually does the work and is called the equipment under control. Includes: valves, pumps, sensors, actuators, compressors, etc.
- Level 1 – Primary Control: These are the control devices, such as programmable logic controllers, that monitor and control Level 0 equipment and safety instrumented systems.
- Level 2 – Area Supervisory Control: Control logic to analyze and act on Level 1 data. Systems include human-machine interface (HMI); supervisory and data acquisition (SCADA) software.
- Level 3 – Site Control: This level includes systems that support control and monitoring functions throughout the plant. Level 3 systems also aggregate lower level data to be transferred to higher level business systems.
DMZ ZONE – separating levels 0-3 and 4-5 4.
- Level 4 – IT Systems: Business logistics systems may include database servers, application servers, and file servers.
- Level 5 – Enterprise Network: The broader set of enterprise IT systems, including connections to the public Internet.
These levels are typically described as creating three logical zones, with levels 4 and 5 comprising the enterprise zone, which is separated from the production zone (comprising levels 0 through 3) by a demilitarized zone (DMZ). This hierarchical approach has worked exceptionally well for OT infra-structure design over the past few decades.
But now a wave of new technologies is now challenging this hierarchical approach to designing and operating OT systems. New technologies include cloud services and 5G wireless networks. More generally, the application of multiple IT solutions to enhance traditional OT has created an entire class of solutions usually referred to as the Industrial Internet of Things (IIoT). The standard IIoT reference architecture consists of three parts.
- The Edge: Includes traditional OT devices, such as sensors and actuators, and the IIoT gateway, which performs a number of tasks such as data filtering, aggregation and storage, and analytics, as well as device management, access control, and shared communications with networks.
- Platform (Cloud): Is typically a Platform as a Service (PaaS), which aggregates data storage and analytics, event processing, process orchestration, network communications, and other functions.
- Enterprise (Enterprise): Supports back-end applications such as databases and data warehouses, application services, etc.
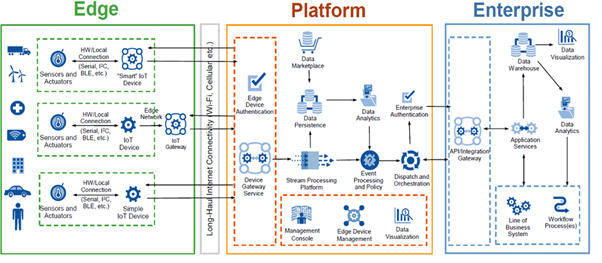
In IIoT deployments, data is not constrained by traditional Purdue hierarchies, and in fact, data no longer resides entirely within the enterprise. The Purdue model can be considered obsolete in these environments. This is because Level 3 is increasingly becoming an intermediate layer that includes both OT and IT components. In this new architecture, the IIoT gateway has become a critical security concern, as a successful attack and security breach of the gateway can put the entire OT infrastructure at risk. Therefore, the European Union Cyber Security Agency (ENISA) has proposed a revised version of the Purdue model that recognizes a Level 3 Industrial IoT (IIoT) platform that communicates directly with Level 1 IIoT devices.

However, it is important to note that IIoT proponents are focused on using new technologies to deliver secure products and services and are not particularly interested in incorporating their solutions into existing architectures. For example, the Industrial Internet Consortium’s IIoT (Volume G4): Security Framework is nearly 200 pages long and never mentions the Purdue model. Ultimately, OT security teams must operate in a world where business imperatives drive technology investment. Modifying or moving away from the Purdue model does not necessarily mean moving away from ICS security, but it does mean that cybersecurity needs to be rethought at every level, and even levels need to be rethought.