Uncategorized
Secure Web Gateway – implementation methodologies
Some say that Secure Web Gateway is a technology that is in its twilight right now. However, organizations still fail to decode […]
Cyber Essentials #6 – Happened… meaning – Incident Reponse
As stressful as it is, in case of reasonable suspicion, assume that a break-in has occurred and start remediation. Relying on hope […]
Cyber Essentials #5 – Ultimately, it’s about data!
Is it about stealing and using them, preventing access to them, declassifying, encrypting or deleting them. Even denial of service attacks are […]
Cyber Essentials #4 – Who accesses what?
In the past, IT resource access protection could not take into account the environment – the walled castle model was popular – […]
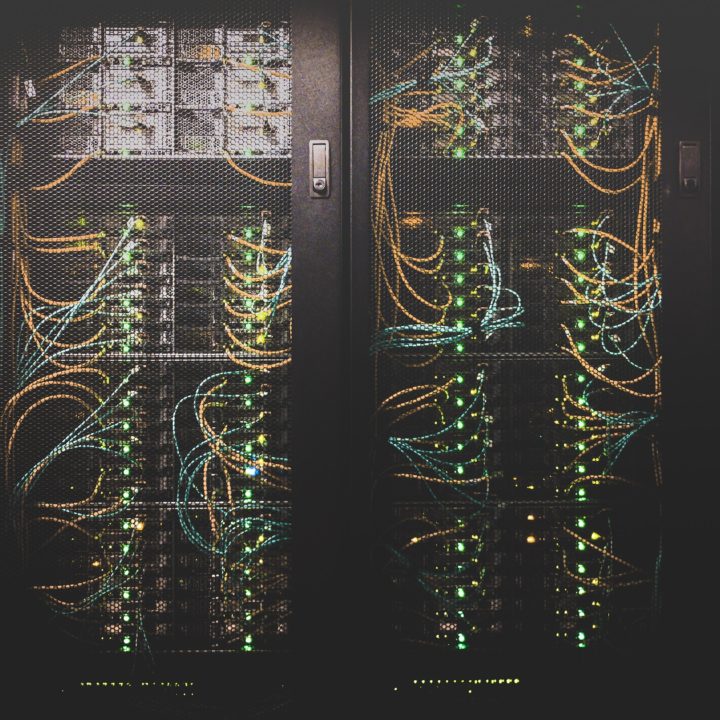
Cyber Essential #3 – Your Systems
Most of the people responsible for cybersecurity -or those who have been relegated to that responsibility because they have broadly understood IT […]