EDR and NDR – efficient protection of IT infrastructure against current threats
Cybersecurity draws in many aspects from military concepts used to combat aggressors on the battlefields. As an example of a military concept transferred to the digital area by Lockheed Martin, we can mention CyberSecurity Kill Chain. Another good example is the SOC Visibility Triad by Gartner. The SOC triad is inspired by the nuclear triad – a concept invented during the Cold War. While the nuclear triad has (thankfully) never been tested, the SOC visibility triad has undergone multiple tests and fulfilled its original purpose – to reduce the likelihood that an attacker will be able to achieve his goals.
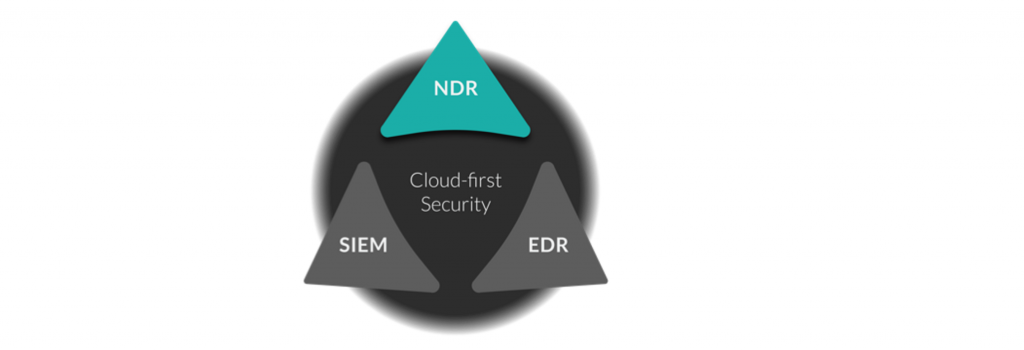
Figure 1: Gartner’s SOC triad
In this article, we will focus on combination of EDR and NDR solutions to answer 2 questions:
- Why did Gartner include EDR and NDR in his triad of SOC visibility?
- What makes the combination of these two solutions provide the visibility necessary to protect the IT infrastructure from current threats?
Let’s start with the fact that SOC teams rely heavily on the MITRE ATT&CK framework for analyzing cyber attacks. Its structure consists of 266 (and continues to grow) Tactics, Techniques and Procedures (TTP) in 12 tactical categories, ranging from the initial break-in, through dodging defense, and finally striking – covering the course of a full cyberattack campaign. MITRE ATT&CK has quickly become the lens through which security teams see their ability to detect attackers’ tactics, techniques and procedures (TTPs). Threat detection and response currently focuses on two main levels – endpoints and network.
Endpoint breaches give attackers access to sensitive information, as well as potential protocols or credentials that may give them further access to the network or more privileged accounts.
Why EDR?
Endpoint Detection & Response (EDR) tools are built to complement traditional endpoint security with enhanced detection, investigation, and response capabilities based on software, processes, and behaviors detected on the endpoint.
It can be said that the EDRs are a camera aimed at the front door.And they are certainly a key element in gaining insight into attack recognition at its first sign.
Unfortunately, due to the enormous volume of information generated by EDR solutions, few companies take full advantage of its value.
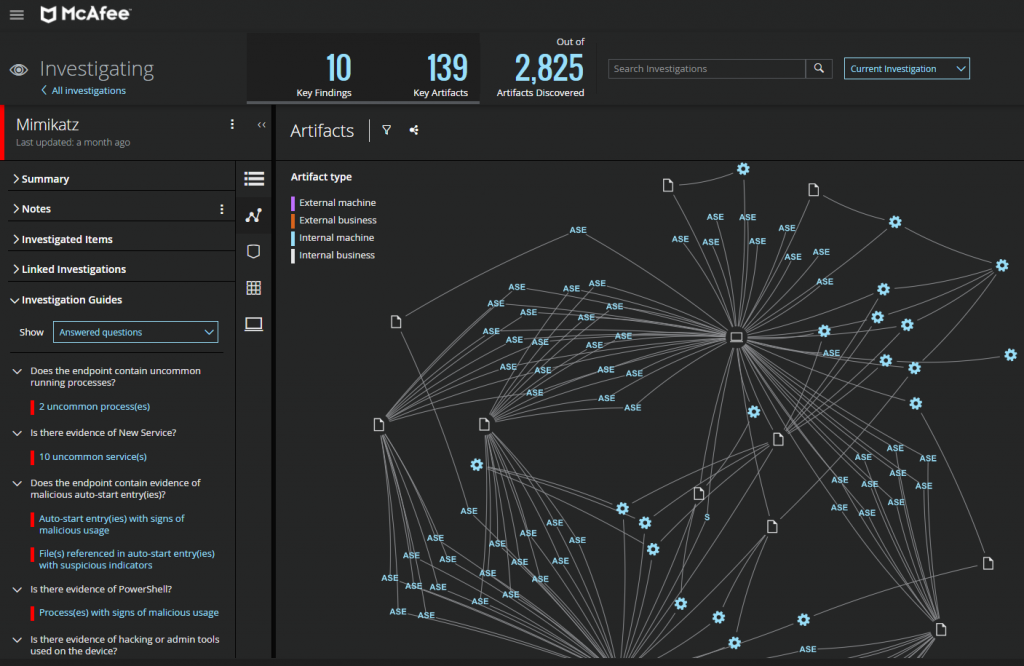
The solution is EDR’s in which the security analyst has support – artificial intelligence, AI. Such EDR can visually correlate detected alerts to create an incident and prioritize them, test hypotheses, handle low-order events, and automate workflows.
There are solutions that can even engage in a dialogue with the user – you can see it in the picture below:
Many companies credits EDR solutions with priority – due to the fact that they are favored by the aforementioned MITRE ATT&C. However, many key tactics, techniques and procedures (TTPs), especially in the later stages of an attack campaign, are easier to spot in the network.
When an attacker found a way into your network and begins to spread inside, making lateral movement from device to device, speed is critical to prevent him advancing. Probably the attacker has already examined some of the security features and found a way to bypass them.
Here are some common ways he can obscure his activities:
- Removing or changing activity logs to mask suspicious behavior.
- Intercepting or launching attacks into unmonitored processes to avoid EDR security.
- Stealing important credentials and using them for unauthorized purposes.
In all of these cases, the attacker buys himself time to expand his reach in the target environment. Security teams that have the ability to detect what happens after this kind of behavior are much more likely to prevent an attacker from achieving their goals.
What is NDR for?
This is where the network threat detection and response system – NDR – Network Detection and Response comes into play. NDR addresses two issues that are critical to overall system security:
- The attacker has to cross the border only once to make the task much easier. Defense-in-Depth is becoming more and more popular, but in 99% of cases, network edge protection is the most advanced one that attacker encounters. Referring to the IRA’s quote after the attempted assassination of Margaret Thatcher, “You must succeed constantly, we only need to succeed once”.
- Edge and endpoint protection mechanisms are visible to the attacker. A quick scan of a compromised laptop can reveal whether EDR is installed on that laptop and whether its activity is being recorded. If the attacker knows the security features, he can plan ahead and target the gaps.
NDR adressess this challenge by observing all communication on the network, including East-West traffic. It is able to detect internal spread, suspicious user behavior, and new, unauthorized devices as soon as they connect. Since NDR platforms acquire data passively, an attacker has no way of knowing if their behavior is being observed or of any mechanism for changing the observation configuration. They can try to avoid detection by encrypting their traffic, but that traffic can be decrypted for analysis or simply blocked if unauthorized encryption schemes, outside the policy, are detected.
READ MORE: The Cognito NDR Platform
What problems does the triad solve for your security team?
The triad of SOC visibility greatly enhances cloud security, but it is worth noting that the triad provides SOC benefits that extend beyond the cloud to edge and on-premises environments.
It does this by providing:
- Visibility: combining visibility in network communication, endpoints and events. The triad allows you to see what is happening in the east-west communication corridor and on the edge of the network.
- Increased discovery: The triad combines rules and signature-based discovery from SIEM and EDR with real-time behavioral discovery based on machine learning from NDR solutions. The result is the ability to quickly detect anomalous behaviors and threats on endpoints and in internal traffic.
- Streamlined computer forensics: With NDR products continuously capturing packets and reassembling them into structured wired data, access to logs from SIEM tools and data from EDR agents, analysts have the full range of information to use in their investigations.
- Automation: With the ability to conduct or support automated or expanded investigations and response, and with the use of artificial intelligence in EDR and NDR, security teams are supported significantly.
- Integration: With NDR products forming the backbone of the triad, SOCs can integrate wired data from network traffic into SIEM and EDR products, as well as between IT and security teams, reducing complexity and tool growth.




